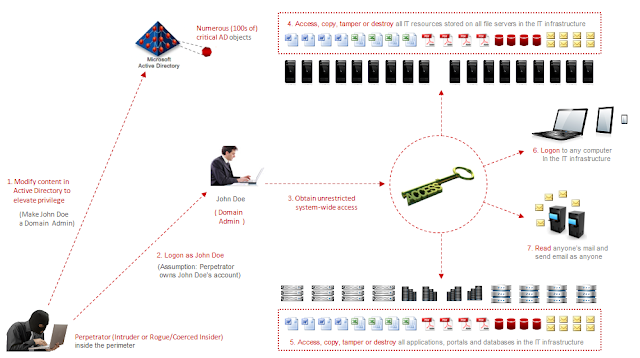
Chaining together Active Directory attack techniques to give your organization the edge against attackers | XM Cyber
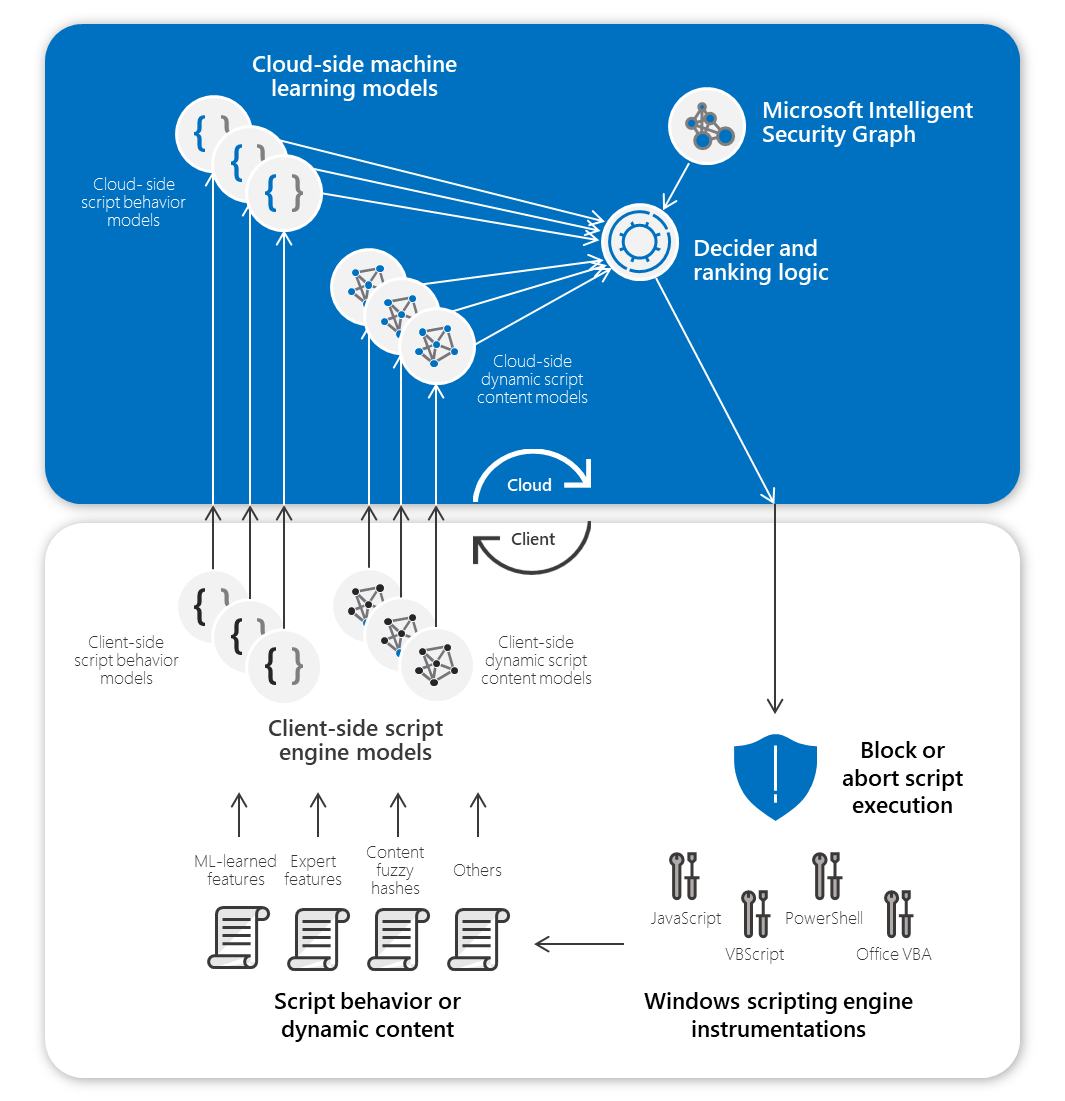
Stopping Active Directory attacks and other post-exploitation behavior with AMSI and machine learning | Microsoft Security Blog
GitHub - infosecn1nja/AD-Attack-Defense: Attack and defend active directory using modern post exploitation adversary tradecraft activity








![Pentester Academy] Attacking and Defending Active Directory Free Download Pentester Academy] Attacking and Defending Active Directory Free Download](https://courseclub.me/wp-content/uploads/2019/07/4564555.png)